Let the upgrades begin
Today, our wish is fulfilled in the form of the Athlon 64 X2 3800+, a dual-core processor running at 2GHz with 512K of L2 cache per core. AMD has priced this baby at $354—significantly less than any of its other dual-core products. It doesn't take a Ph.D. in computer engineering to figure out that the X2 3800+ ought to offer a very potent combo of price and performance.
As is our custom, we compared the X2 3800+ against over a dozen single- and dual-core competitors to see just how it fits into the big picture. Then we overclocked the living daylights out of the thing, and everything went soft and fuzzy. Our heads are still spinning. Keep reading to see why.
Code name: Manchester
Our first exposure to the Athlon 64 X2 came in the form of the 4800+ model. That chip is code-named "Toledo," and it packs 1MB of L2 cache per processor core, as do the dual-core Opterons. Toledo-core chips sport a transistor count of about 230 million, all crammed into a die size of 199 mm2.
AMD also makes several models of Athlon 64 X2 that have only 512K of L2 cache. In the past, CPUs with smaller caches have sometimes been based on the exact same chip as the ones with more cache, but they'd have half of the L2 cache disabled for one reason or another. That's not the case with the X2 3800+. AMD says this "Manchester"-core part has about 154 million transistors and a die size of 147 mm2, so it's clearly a different chip. AMD rates the max thermal power needed to cool the X2 3800+ at 89W—well below the 110W rating of the 4800+—and they've revised down the max thermal power of the X2 4200+ to 89W, as well. The Manchester core is obviously a smaller, cooler, and cheaper-to-manufacture chip than Toledo.


The Athlon 64 X2 3800+ Cosmetically, though, you'd never know it, because the X2 3800+ looks like pretty much any other Socket 939 processor. The X2 3800+ is intended to work with AMD's existing Socket 939 infrastructure, and it may well be an upgrade option for current owners of Athlon 64 systems. You'll want to check with your motherboard maker to see whether or not your board will support an X2 before making the leap, though. Some boards need only a BIOS update, but we're finding out that some others just can't handle X2 processors. Most newer motherboards should be fine.
Before we dive into the benchmark numbers, let's have a quick look at where the X2 3800+ fits into the bigger picture. With its introduction, the Athlon 64 X2 family now looks like so:
| CPU | Clock speed | L2 cache size | Price |
| Athlon 64 X2 3800+ | 2.0GHz | 512KB | $354 |
| Athlon 64 X2 4200+ | 2.2GHz | 512KB | $482 |
| Athlon 64 X2 4400+ | 2.2GHz | 1024KB | $537 |
| Athlon 64 X2 4600+ | 2.4GHz | 512KB | $704 |
| Athlon 64 X2 4800+ | 2.4GHz | 1024KB | $902 |
At $354, the X2 3800+ isn't exactly cheap, but it does extend the X2 line into more affordable territory. You've probably noticed the apparent hole in the X2 models at 4000+. Logic would dictate that the X2 4000+ would run at 2GHz and have 1MB of L2 cache. So where is it? I asked AMD this very question, and they told me that they won't comment on unannounced products—and besides there aren't any plans for an X2 4000+ right now.
I'm not too broken up about that, because I'm not convinced the additional L2 cache is worth paying more money to get. We'll address that issue in more detail when we look at the benchmark results.
Now for something really confusing. How does the Athlon 64 X2 3800+ stack up against the competition? Figuring out such things has become horribly puzzling as Model Number Mania has taken hold of the CPU market. Here's my attempt at lining up the various AMD and Intel CPU models according to rough price parity:
| CPU | Price | CPU | Price | CPU | Price | CPU | Price | CPU | Price |
| Pentium 4 541 | $218 | Pentium 4 630 | $224 | Athlon 64 3200+ | $194 | ||||
| Pentium 4 551 | $278 | Pentium 4 640 | $237 | Pentium D 820 | $241 | Athlon 64 3500+ | $223 | ||
| Pentium D 830 | $316 | Athlon 64 3800+ | $329 | Athlon 64 X2 3800+ | $354 | ||||
| Pentium 4 561 | $417 | Pentium 4 650 | $401 | Athlon 64 4000+ | $375 | ||||
| Athlon 64 X2 4200+ | $482 | ||||||||
| Pentium D 840 | $530 | Athlon 64 X2 4400+ | $537 | ||||||
| Pentium 4 571 | $637 | Pentium 4 660 | $605 | Athlon 64 X2 4600+ | $704 | ||||
| Pentium 4 670 | $851 | Athlon 64 FX-55 | $827 | ||||||
| Pentium 4 XE 3.73GHz | $999 | Pentium XE 840 | $999 | Athlon 64 FX-57 | $1031 | Athlon 64 X2 4800+ | $902 |
From this handy table, we learn that the X2 3800+'s dual-core competition from Intel is probably the Pentium D 830. You can have a single-core Pentium 4 551 for about 75 bucks less than the price of the X2 3800+, or you could pick up AMD's single-core Athlon 64 3800+ in the same basic price range as the "equivalent" X2. The Athlon 64 3800+ runs at 2.4GHz and has a 512K L2 cache, so you lose 400MHz and pick up a whole second CPU core by going for the X2 3800+ instead. I'd say that's an easy tradeoff to make, but the benchmark results will tell us more about the shape of that choice.











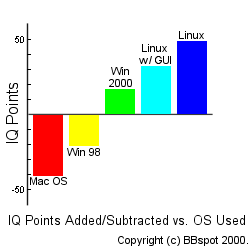 "Programmers have worked very hard in the latest kernel release trying to make even simple tasks more difficult," continued Mr. Klens, "This release is going to include the "ocsh" - the obfuscated C shell, sure to be a favorite of intellectual superiors. In addition to inputting commands as obfuscated C code, users can also input commands in binary directly to the registers. It took me 10 minutes to code the directions to 'cat' using ocsh, but it was worth it!"
"Programmers have worked very hard in the latest kernel release trying to make even simple tasks more difficult," continued Mr. Klens, "This release is going to include the "ocsh" - the obfuscated C shell, sure to be a favorite of intellectual superiors. In addition to inputting commands as obfuscated C code, users can also input commands in binary directly to the registers. It took me 10 minutes to code the directions to 'cat' using ocsh, but it was worth it!"